Create a Google Cloud Service Account and Grant Access
Overview
This topic discusses how to create a service account manually within Google Cloud so the Lacework integration can use it.
Create a Service Account
For more information, see Google Cloud documentation about creating and managing service accounts.
Follow these steps to create a service account:
Log in to the Google Cloud Console.
Go to the IAM & Admin page, then click Service Accounts > + Create Service Account.
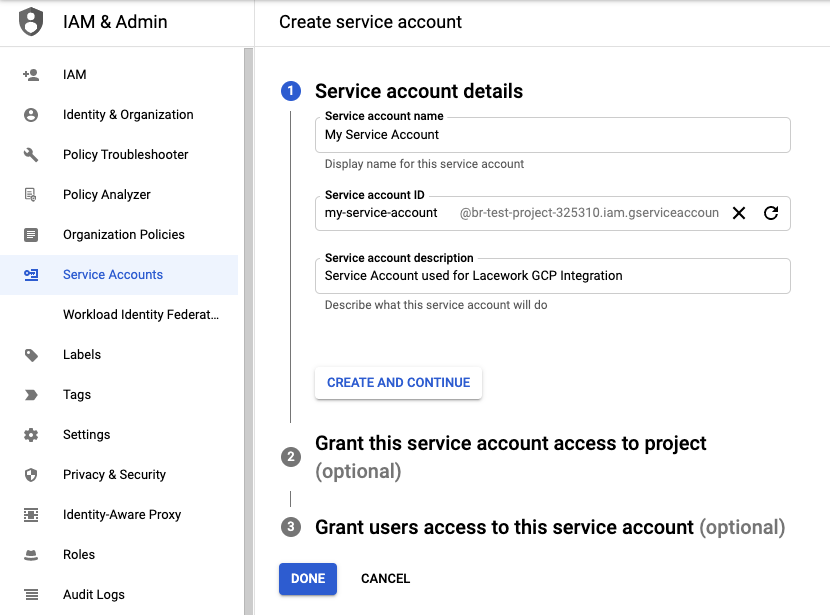
In the Service account details step, enter values in the fields, then click Create and Continue.
Skip the optional sections and click Done.
On the Services Accounts page, find the newly created service account, click the menu under Actions, and click Manage keys.
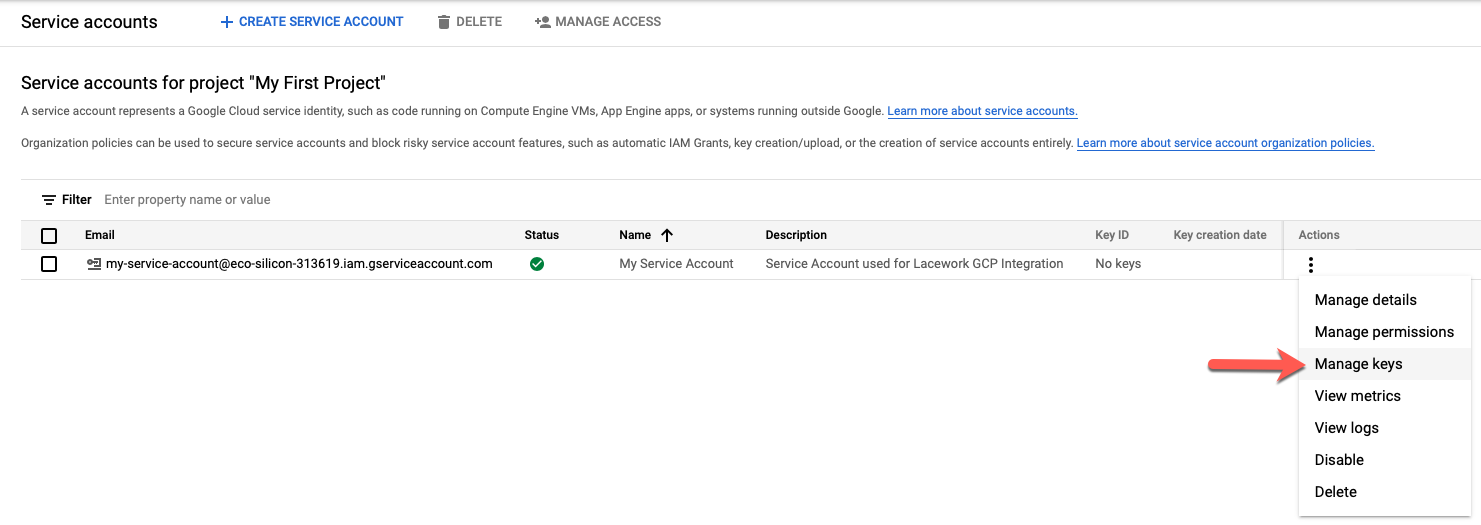
Click Add Key > Create new key.
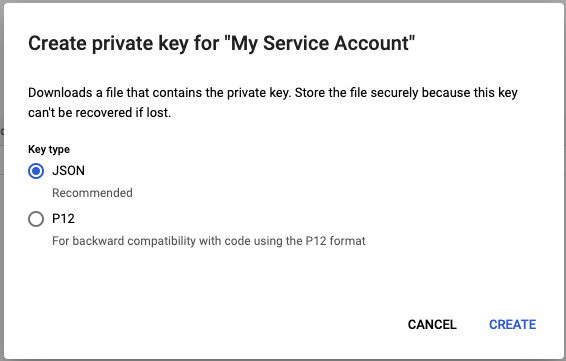
Select the JSON key type, then click Create. A JSON key file downloads to your system.
 note
noteAfter you download the key file, you cannot download it again.
In the Details tab, find the email address of the new service account and copy it to your clipboard.
Click the menu icon located at the top right of the page to exit the Service Accounts page.
(Configuration Only) Create the Lacework Configuration Custom Role
This step is required only when creating a Lacework Configuration compliance integration.
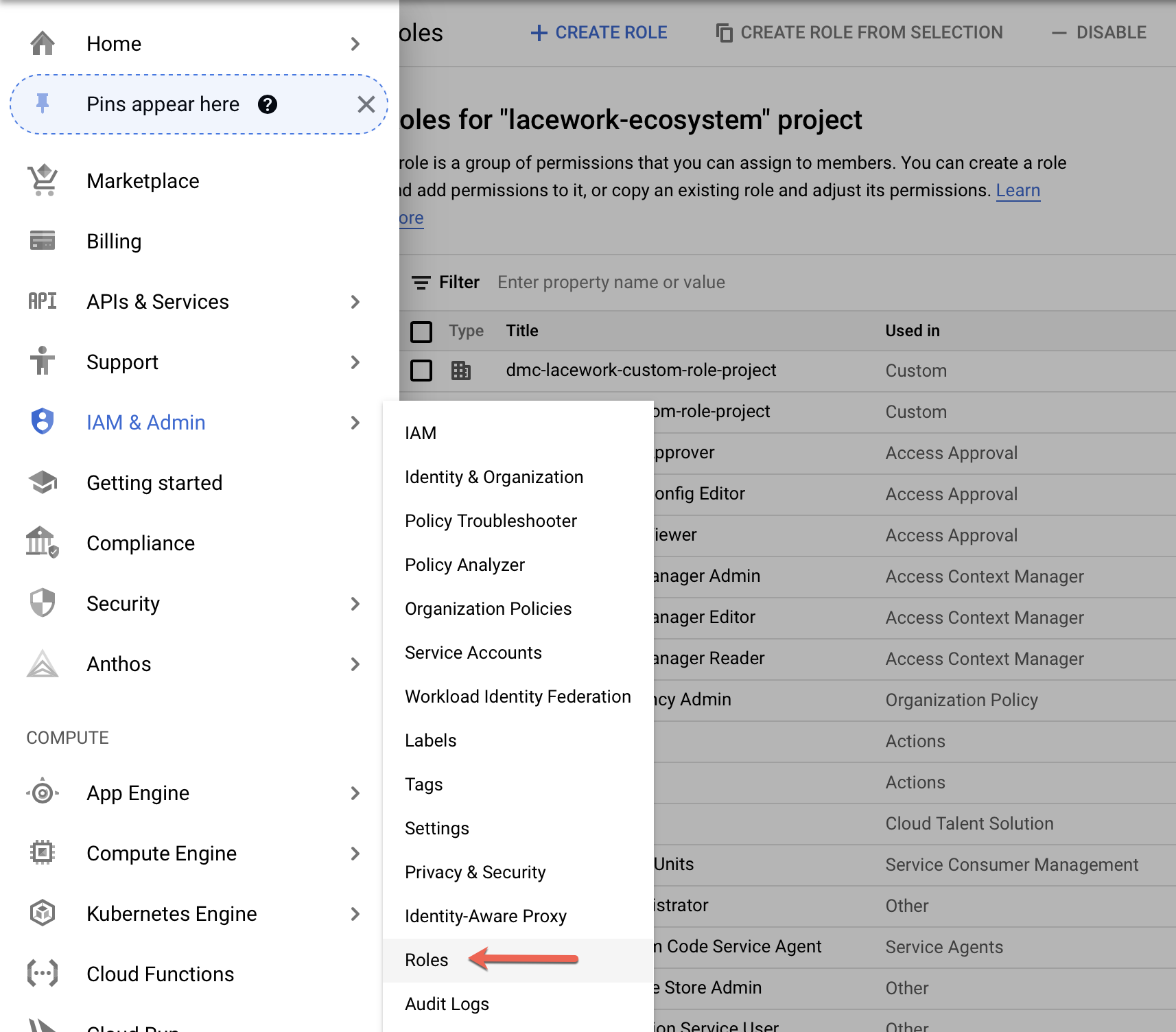
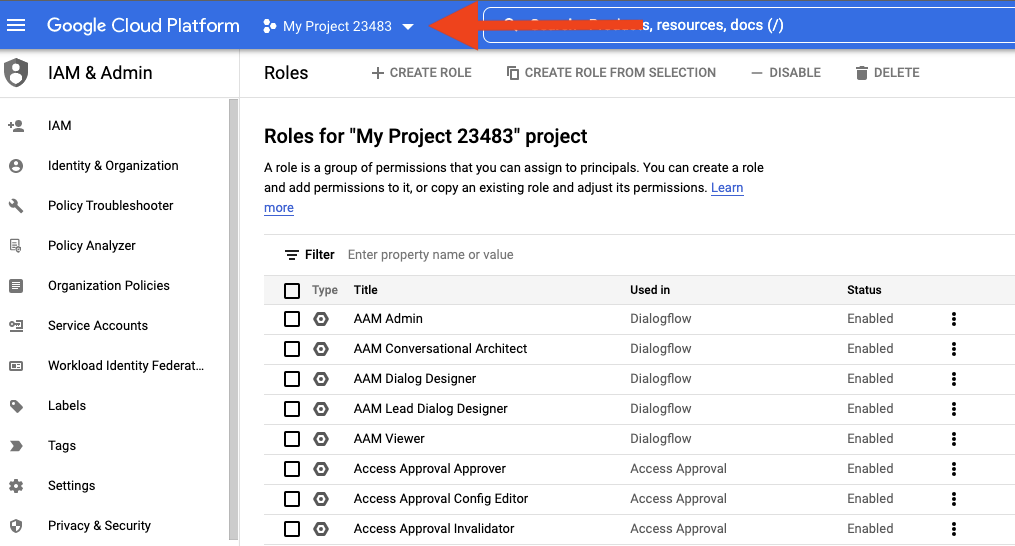
Select IAM & Admin > Roles from the cloud console navigation menu.
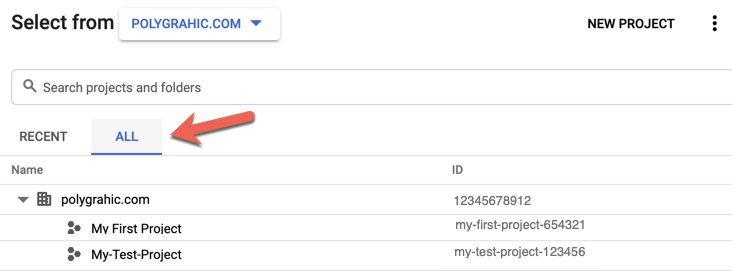
Click the down arrow in the top menu bar for the project.
The Select from dialog appears.
From the Select from drop-down, select an organization that contains the Google Cloud resources that you want the integration to monitor, or select
No Organizationif selecting a project that does not reside within an organization.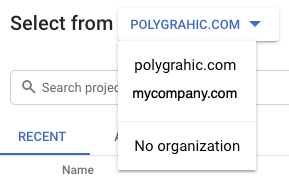
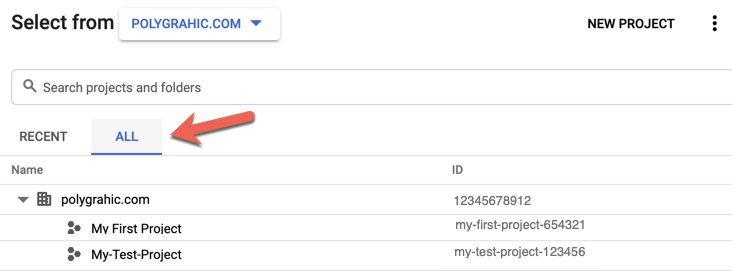
In the Select from dialog, click the All tab to display the list of all entities. Select the organization or project where the custom role will be created, then click Open.
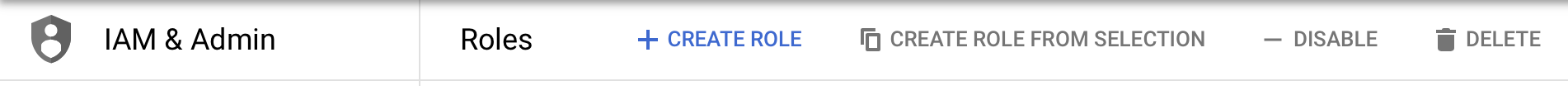
Click Create Role on the top toolbar.
In the Create Role page, enter a title, description, and account identifier. From the Role launch stage drop-down, select General Availability.
Lacework suggests naming similar to below.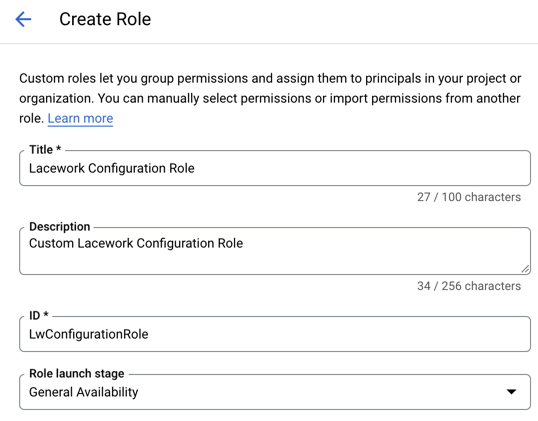
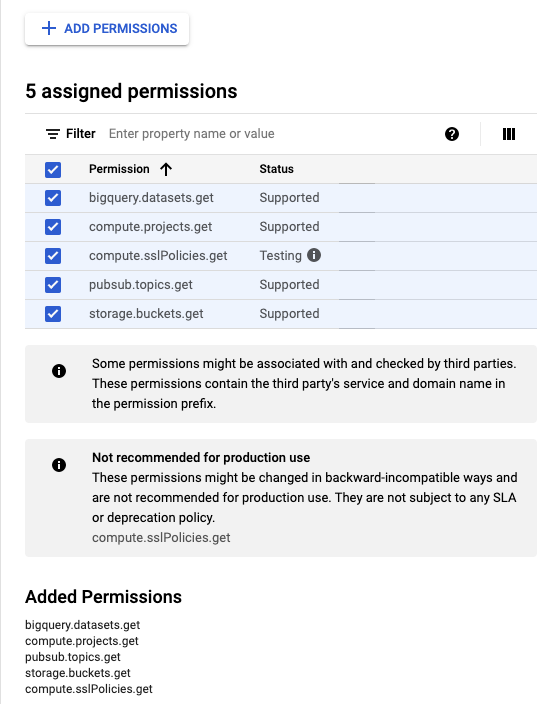
Add the required permissions by clicking + Add Permissions.
Click Create.
Grant the Required Roles to the Service Account
Grant the required roles to the service account created in the previous section:
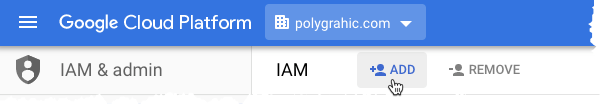
Select IAM & Admin > IAM from the cloud console navigation menu.
Click the down arrow in the top menu bar for the project.
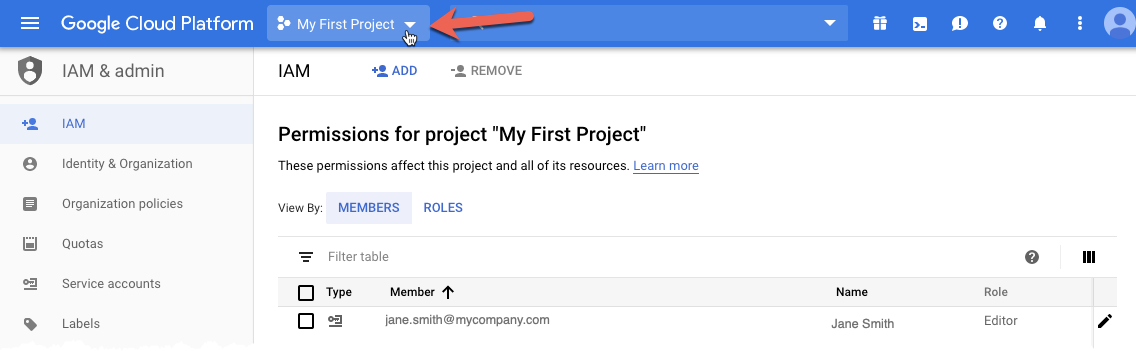
The Select from dialog appears.
From the Select from drop-down, select an organization that contains the Google Cloud resources that you want the integration to monitor, or select
No Organizationif selecting a project that does not reside within an organization.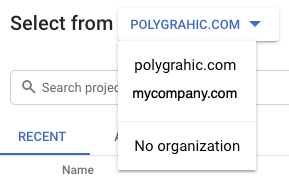
In the Select from dialog, click the All tab to display the list of all entities. Select the organization or project where the IAM roles will be granted, then click Open.
Click Add.
noteYou must have permission to add members to the organization or project IAM policy for the Add button to be active.
Add a member and roles to a project or organization. In the New members field, paste the email address of the service account copied in an earlier step.
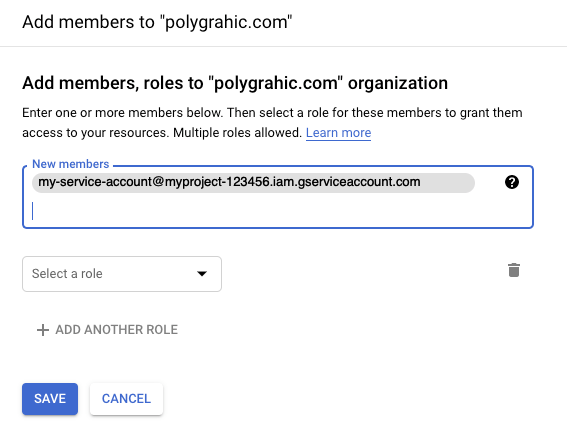
From the Select a role drop-down, select the appropriate roles depending on the integration type.
(Configuration only): Add the custom role created from the Create the Lacework Configuration Custom Role section.

Click Save.
Service Account Roles
These are the specific roles required by the service account being used for an integration, depending on the integration type and level.
Configuration Integration
The following roles are required by the service account for a configuration integration:
| Role Name | Role ID | Integration Level |
|---|---|---|
| Organization Viewer | roles/resourcemanager.organizationViewer | Organization |
| Browser | roles/browser | Organization and project |
| Cloud Asset Viewer | roles/cloudasset.viewer | Organization and project |
| Security Reviewer | roles/iam.securityReviewer | Organization and project |
| Custom role for Lacework configuration integration | Custom role with permissions listed in Lacework Configuration Role Permissions. For instructions on creating the custom role, see Create the Lacework Configuration Custom Role. | Organization and project |
Pub/Sub-Based Audit Log Integration
The following roles are required by the service account for a Pub/Sub-based audit log integration:
| Role Name | Role ID | Integration Level |
|---|---|---|
| Browser | roles/browser | Organization |
| Monitoring Viewer | roles/monitoring.viewer | Organization and project |
| Pub/Sub Subscriber | roles/pubsub.subscriber | Organization and project |
Storage-Based Audit Log Integration
The following roles are required by the service account for a Storage-based audit log integration:
| Role Name | Role ID | Integration Level |
|---|---|---|
| Organization Viewer | roles/resourcemanager.organizationViewer | Organization |
| Storage Object Viewer | roles/storage.objectViewer | Organization and project |
| Pub/Sub Subscriber | roles/pubsub.subscriber | Organization and project |
Lacework Configuration Role Permissions
In addition to the above Google Cloud roles, Lacework also requires a custom role for the Configuration integration. The permissions required are outlined in the following table:
| Role Name | Permissions | Usage |
|---|---|---|
| Lacework Configuration Role | bigquery.datasets.get | Read access to retrieve dataset metadata, such as encryption keys and access permissions. |
compute.projects.get | Read access to project metadata, such as the resources contained within. | |
pubsub.topics.get | Read access to Pub/Sub topics metadata. | |
storage.buckets.get | Read access to bucket metadata, excluding IAM policies. Can also list or read Pub/Sub notification configurations on a bucket. | |
compute.sslPolicies.get | Read access to SSL policy resources. |